MMD-0018-2014 - Analysis note: "Upatre" is back to SSL?
03 Apr 2014Latest Progress/Changes/Updates:
#Malware Info - #Upatre changed its USER-AGENT header (pic)
/cc: @node5 @EmergingThreats pic.twitter.com/uCOGmP1EIQ
— MalwareMustDie, NPO (@MalwareMustDie) April 24, 2014#Upatre/#Zeus GMO #Spambot IP Report/April 2014 http://t.co/dZIxerUYbt
Session=112, Uniq IP/Alive=102/38 < 41 cntry, top=USA
#MalwareMustDie
— Hendrik ADRIAN (@unixfreaxjp) April 26, 2014The background
Following the previous blog (link) of Zeus P2P Gameover (GMO) malware delivered by the Upatre trojan downloader from some encrypted form with varied file extension names. Today I found that the threat returned to previous model of Upatre downloader scheme (via SSL). Just in case I post it here, is not a new stuff, hope can help some friends:
The spam sample is like this:
*) The attached executable samples can be viewed at the bottom of this post.
The Upatre binary analysis
Some notes of the attached archived PE:
Compile Time: "0x533C67DB [Wed Apr 02 19:41:15 2014 UTC]"I also use our beloved PeStudio downloaded from winitor.com for the reliable alert's check:
Identified compiler : "Microsoft Visual C++ 5.0/6.0"
Entry Point at section: ".text"
CRC Fail: "Claimed 90984, Actual 77672"
Sigs: "Verified:Unsigned, Publisher: n/a"
Bad Entropy: ".text
Flags: IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ
Entropy: 6.336388 (Min=0.0, Max=8.0)
MD5: 28f4e63b3406fb9343aaf369f1897fb0"
Some suspicious/blacklisted calls used:
" GetStartupInfoW .rdata: 0x000035D8,kernel32.dllSo.. combined with the below's system's used "internals calls"... this "software" is likely never good..
GetModuleHandleW .rdata: 0x000035C4,kernel32.dll
_controlfp .rdata: 0x000035B6,msvcrt.dll"
// Note about MSVCRT.DLL
is the Microsoft Visual C Run-Time Library (and MSVCPP.DLL is the standard C++ library)
for Visual C++ version 4.2 to 6.0. It provides programs compiled with these versions o
f Visual C++ a typical set of library functions required by C and C++ programs. These i
nclude string manipulation, memory allocation, C-style input/output calls, etc. The msv
crt.dll is now a "known DLL," meaning that it is a system component owned and built by
Windows. It is intended for future use only by system-level components.
"_wcmdln .rdata: 0x0000351A,msvcrt.dll...But yet, some known software made by Microsoft Visual C also having the traces of them, hmm..I'll stick to "suspicious" then :
__wgetmainargs .rdata: 0x00003524,msvcrt.dll
_initterm .rdata: 0x00003536,msvcrt.dll
__setusermatherr .rdata: 0x00003542,msvcrt.dll
_adjust_fdiv .rdata: 0x00003556,msvcrt.dll
__p__commode .rdata: 0x00003566,msvcrt.dll
__set_app_type .rdata: 0x00003584,msvcrt.dll
_except_handler3 .rdata: 0x00003596,msvcrt.dll
_XcptFilter .rdata: 0x00003504,msvcrt.dll
__p__fmode .rdata: 0x00003576,msvcrt.dll"
@MalwareMustDie Almost! I'll try to find another one. pic.twitter.com/QBrYFdW7wH
— Marc Ochsenmeier (@ochsenmeier) April 3, 2014The Upatre binary contains encrypted (or obfuscated?) data in here:
.text:00401870 dd 498D10h, 0F1708305h, 0FF8B04h, 0AC7FF60h, 8D0004E8hNote: I tend to call it encrypted since it needs a XOR key to decrypt it. There are some more obfuscated data in other places too (in .data, .rdata, and .rsrc), but this binary is a case of encrypted PE.
.text:00401870 dd 45C150CCh, 8BFFFF8Dh, 0F811082h, 4242483h, 6F006300h
.text:00401870 dd 8B01E8FFh, 40420D4h, 8D00248Bh, 0F8107D83h, 3300E8FFh
.text:00401870 dd 0F8037E01h, 48B24E8h, 2025A09h, 8B018D8Dh, 412C00h
.text:00401870 dd 0FFFF33FFh, 0DC188261h, 12401FFh, 0A00C0408h, 8BFF0104h
.text:00401870 dd 700C150Dh, 1FF2400h, 0F4F022DBh, 8B000133h, 0E17300E1h
[...]
.text:00401870 dd 2 dup(1F001Fh), 0FF00001Fh, 324B32h, 13E08D00h, 0FF1F001Fh
.text:00401870 dd 2 dup(1F001Fh), 0
.text:00401C54 dd 68014816h, 3 dup(1F001F00h), 0FF1F001Fh, 0F06492h, 2 dup(1F001Fh)
.text:00401C54 dd 0FF001Fh, 1F1FFF00h, 4026F155h, 2 dup(1F001F00h), 0A201A241h
.text:00401C54 dd 1F001Fh, 6E614865h, 1F00FF00h, 1FFFh, 2 dup(1F001F00h)
.text:00401C54 dd 0E815701h, 1C001014h, 4081804h, 100008h, 18080404h
[...]
.text:00401C54 dd 0C900F8h, 0D400EAh, 0ED00E0h, 0D000C9h, 0AA0095h, 890076h
.text:00401C54 dd 6C0093h, 83007Ch, 8F0070h, 0D100EEh, 94002Bh, 0C600F9h
.text:00401C54 dd 60079h
.text:0040229C db 0C0h, 0 // closing chunk.
If we solve the above obfuscation (which I can not) it should give codes for method to decrypt the encrypted traffic, downloads malware from assigned hosts. If you don't have disassembly you can use the raw disassembler result from IDA free version I pasted here--> (link) to start the reversing process.
Another note: the "start" point is in .text section, it checks environment there (plus few evasion tricks) and go to wWinMain which contains the real deal of decrypting the obfuscated data. In the wWinMain I can see a below interesting checking pattern after XOR:
"deobfuscation pattern, repeated more than one..
(three times actually with different used registers")
[...]
push edi
pop edx
mov eax, [ebp+var_60]
rol eax, 6
add eax, 455E4A5h
mov [ebp+var_3C], eax
mov edx, 136C6E9Bh
mov [ebp+var_1C], edx
mov ecx, 7E0C0B9Ah
mov [ebp+var_68], ecx
mov eax, 668758F1h
mov [ebp+var_14], eax
mov edx, 5D1E4FCDh
mov [ebp+var_18], edx
mov ecx, 0FFFFFFFFh
mov [ebp+var_C], ecx
call sub_4015A0 [...] <=== "xor'ed and checked"
"called checks to sub_4015A0: "
push ebx
push esi
push edi
mov ebx, [ebp-80h]
xor ebx, 0ABED8791h <======
mov edx, 40000000h
ror edx, 0Eh
cmp ebx, edx // the checks.
jb sub_401464 // end stuff here...
How does it work?
This is what I saw. The Upatre during execution is communicating to below host:
kionic,com / 64,92,125,121 (Netfronts/U.S.A.)
via TLSv1 (SSL):
which fetching the microsoft certification patch's URL and Comodo's encryption certification's URL:
Next, these data will trigger each URL in the list to be downloaded by the Upatre itself as per shown below:
Some reference for you of the explanation what was downloaded from the microsoft site:
Is a patch to revoke certification, was intended to make sure the following Comodo certification can be installed successfully:
This is the one that can be downloaded successfully:
Next.. Upatre downloads a binary blob via an encrypted communication (SSL) from kionic.com (64.92.125.121):
To be more viewable: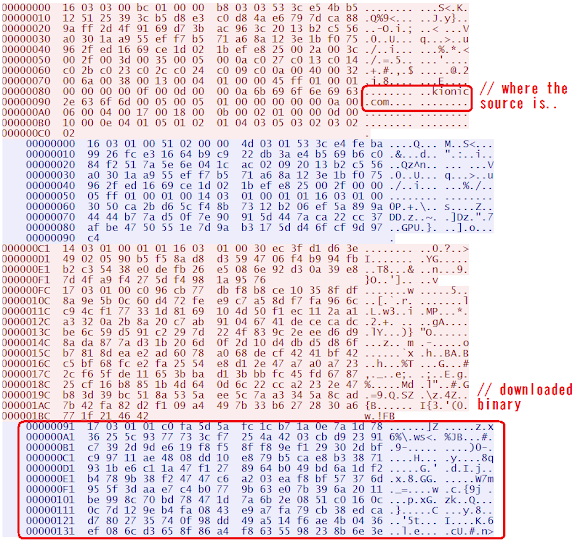
The downloaded malware is to be saved and registered (autorun) in:
// drops:it is Zeus P2P Gameover (GMO) with rootkit version. Upatre execute this GMO and self deleting itself. Clean cut.
C:\Documents and Settings\%USER%\Local Settings\Temp\Ixtya (RANDOM)
2004/08/08 12:58 646,656 dyzucy.exe (random) 0929a17a3fbaf6b1eb63ab8d5edbdd45
// registry..
Key: HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\Run
Data: "dyzucy.exe" (RANDOM), Values: "C:\Documents and Settings\kaspersky\Local Settings\Temp\Ixtya (RANDOM)\dyzucy.exe(RANDOM)"
Spawned malicious processes is like this:
Invoice_040314.scr (PID: 3860 MD5: C941E2997DC2A1E39515D226E1830DB4)
tech3.exe (PID: 1192 MD5: 984A0B8A58EA60B3376CE25692B68FA8)
tech3i.exe (PID: 3672 MD5: 5038C8E8D2B9A00327D0CBF334223E9D)
dyzucy.exe (PID: 1404 MD5: C7BD551912375FA2312629E070AC51F2)
1aaa970c.sys (PID: 4 MD5: BA2B9FFB336BF5AF0247313FE2509435)
cmd.exe (PID: 4076 cmdline: C:\Windows\system32\cmd.exe /c %Temp%\XNY9C82.bat MD5: AD7B9C14083B52BC532FBA5948342B98)
The Gameover
Not much to tell (kudos good people who fight this threat well!), instead is an usual installation (the batch), and drops its rootkit & hooked itself in registry, after a while it starts querying some DGA as below:
aulbbiwslxpvvphxnjij,biz 50.116.4.71 / li430-71.members.linode.com..and as usual it sent a POST /write HTTP/1.1 (I don't go to details on these, cheers!):
behatwdxzxelembmfahkw,biz 198.58.99.149 / li532-149.members.linode.com.
behlznftlhyhguozcmadahadykr,info
cirwfqwscqgukqsxwonxwfatuk,info
dgmvgggqdvsxrfiwaqtsztbqt,com
empxryuofimvoztuwxdizt,org
fkrbzlcqhhmswfmcqxwxvvwmfb,biz
fmvljpnvrkwvsclztcfdrg,biz
inqstkjrucdatosodzdbmjamso,org
mbdhuzovxojtbijfifqkzpdgy,com
mbmvtofijddzkbjnbyciulf,ru
pdmifxljinvgdmxgzlimvvscuy,com
pfyplvyrvnztwuscaimffigunr,net
qkjnbenbgeqsyhhpmfpvaywcwg,org
rgpfypqszdudswglgiofjzxx,ru
roovifjnyxhqcdyeisqghpfpov,net
tovlcydmawtgpbhqttqsk,ru
vskljhldscxnaievoqk,net
xctduwmfaubminhlftcbyvojgehe,com
xyxkdmzvclnylaqeykrtougqc,info
zlhqsfqjnqwvseapwkeahegioj,com
Are they really changed?
Ah, the "ZZP" #Upatre also stays :-)
VT: https://t.co/jCUThBKiSX
#MalwareMustDie! pic.twitter.com/q7yUmpMYzp
— MalwareMustDie, NPO (@MalwareMustDie) April 3, 2014Samples, Traffic and VT
Below is the sample's snapshots:
Please download via Kernel Mode-->(link)
Matrix of stages infection's detection ratio (VT)
This time I would like to make a matrix of the detection ratio of the malware by the time I analyze this sample. I used the VirusTotal (VT) scores for the comprehensive result purpose. Please be noted that VT score is based on part of signature (not overall filtration and) detection used by AntiVirus industry, so it is just not an exact measurement, but is good enough to give the idea of how is the detection on this threat by AV industry in every form of samples (during infection stages) on this infection.
The "Stages" column explained the form of the malware during the infection process as the object to be scanned by AV products. I started from the stage 1 as the email data itself, goes to the attachment in zip, PE, PE self copied after being clicked, the downloaded GMO, self-copied GMO and rootkit downloaded/used. Feel free to comment for improvement:
| Stages | Malware | Virus Total Score |
| 1 | EML Spam file | 15/51 |
| 2 | Upatre SCR in attached zip | 21/51 |
| 3 | Upatre fake SCR the PE file | 20/51 |
| 4 | Upatre Self-Copied after clicked | 14/51 |
| 5 | Downloaded Zeus GMO | 17/51 |
| 6 | Self-Copy Zeus GMO after downloaded | 13/51 |
| 7 | Rootkit (Necurs) | 15/51 |
So in overall we have an average score 16.42/51 or 32.21% detection ratio for this malvertisement, not so bad :-)
Where are those Spambots??
We are lunching the Upatre Spambot monitoring, these spambots are infected PC which are scattered all over the world, like below samples I tweeted:
Upatre Spambot in Spain (pic)
@Panda_Security @jcanto @belmontemartin @a0rtega pic.twitter.com/FMS681fjVs
— MalwareMustDie, NPO (@MalwareMustDie) April 24, 2014Found Zeus Gameover Spambot in Japan (pic)
This is it. Any LE want to nail THESE pricks seriously? Give me time line! pic.twitter.com/as2ZY42yuR
— MalwareMustDie, NPO (@MalwareMustDie) April 24, 2014And also relayed from Russia itself (pic)
(Upatre/Gameover ) https://t.co/ud1X5FFSCD
Cc: @CERTGIB @ESET pic.twitter.com/noQrriVOJy
— MalwareMustDie, NPO (@MalwareMustDie) April 24, 2014We recorded all of the Upatre malvertisement in session with our own SMTP honeypot. We decided to share the infected IP addresses for the ISP and CERT of each country to do the clean-up. The April 2014 Statistic for Upatre spambot infected PC was released, as per announced in below tweet, we will try to manage to update this data periodically.
#Upatre/#Zeus GMO #Spambot IP Report/April 2014 http://t.co/dZIxerUYbt
Session=112, Uniq IP/Alive=102/38 < 41 cntry, top=USA
#MalwareMustDie
— Hendrik ADRIAN (@unixfreaxjp) April 26, 2014Video Analysis Tips and Guide
I made & upload an HD Video as a quick way of howto analyze this threat (Upatre/GameOver sets) as per seen below. I use the different set of sample and is not describing the specific sample mentioned in this or previous post, but same threat and case:
Further "rtrace" Reversing by @nullandnull
#Malware #reversing Upatre, rtrace & XP EOL http://t.co/gaWbld9ZGb by @nullandnull < Bravo Alex! #w00t for rtrace♥ & #malwaremustdie mention
— Hendrik ADRIAN (@unixfreaxjp) April 20, 2014Stay safe friends. #MalwareMustDie!